What Is Dark W

If you are interested in hacking and looking for active deep web links for knowing about hacking tips, hacking services offered at deep web and hackers groups also, then you will love to explore the below collection. Lots of activities are performed on the deep web related to hacking daily. Below I am sharing some […]
What is Important when we are configuring Office 365 for enterprises or businesses?

First of all, we need a Microsoft office 365 subscription with admin Credentials, When we subscribe to Microsoft Office 365 service, Microsoft provides admin credentials to us like Username: xyz@domain.onmicrosoft.com Password: xyW@#123axsdT Login Using these credentials to the Microsoft Office 365 admin console from here you need to add your domain to start service on your own, […]
Ransomware Code For Learning Purpose Only
It is a virus which encrypt your data with Ransome key post attack of Ransomware all data is get stuck and it cannot be retrieve without Ransome key it is the Dangerous Malware Of The Decade it is not removable or destroyable as a professional I get a chance to interact with live Ransome attack […]
Types of Network Security

Majour and Important types are as follows : 1.Access Control In this case not every person should have a complete allowance for the accessibility to network & its data. Access is given as per the user’s rights. 2.Antivirus & Antimalware Software […]
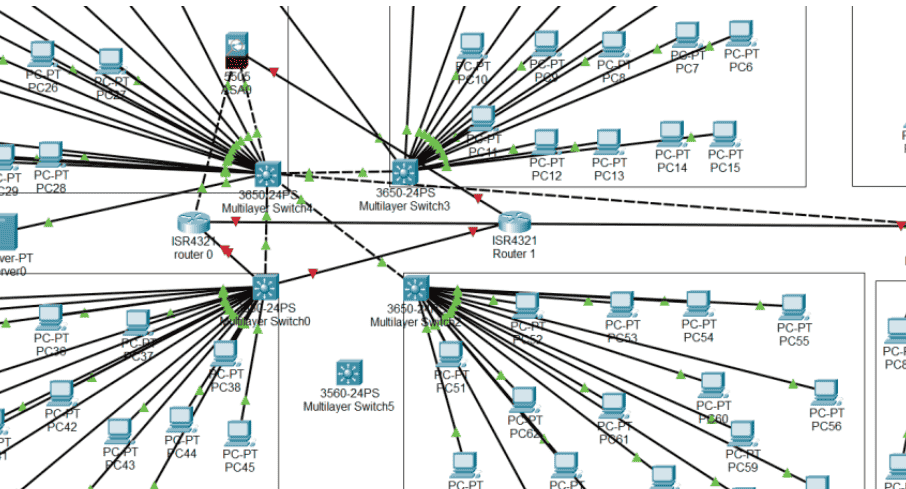
Switching

Switching is the process of transferring data packets from one device to another in a network or from one network to another network using a specific device that is called SWITCH. User experience switching all the time for example accessing the internet from your computer device where a user requests a webpage to open the […]
How Nmap Works?
Nmap is an Information Gathering tool which scans targeted Ip and provides Port Specification, Services, Operating System Detection, Scripting Engine (NSE), Aggressive scanning, Output Verbosity, Miscellaneous options. After doing this scan we get vulnerability in the target and then real game start to hack. Let’s See how Scan works with commands: nmap 192.168.1.1 Here’s an example […]
